Automatic Permissions generated by GeneXus with GAM and permissions that can be created by the administrator user of the GAM Backend are used in the GeneXus code to let only authorized users access the different resources of an application.
In the case of Automatic Permissions, GeneXus generates the permissions in F5. At runtime (when the object is going to be executed), it checks if the user has the permission, or if he has a role where the permission is included. This happens for those objects which have Integrated Security Level set to "Authorization". So, this property value has to be set for all the objects that are going to generate permissions which are checked at runtime.
When permissions are going to be created by the GeneXus user and are used programmatically, the object does not need to have Integrated Security Level set to "Authorization" because "Authentication" is enough.
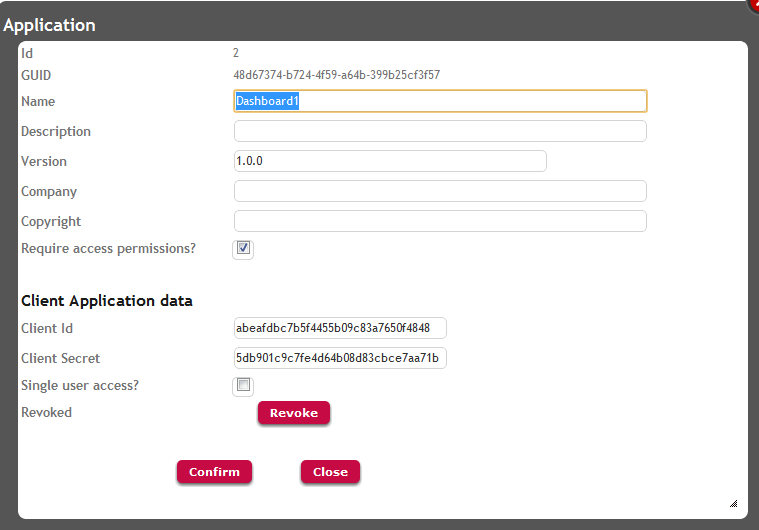
The only prerequisite is that Require Access Permissions of the GAM Application is checked.
The following is an example where a permission is defined using the GAM Backend, in order to restrict the visualization of a grid column in an SD panel.
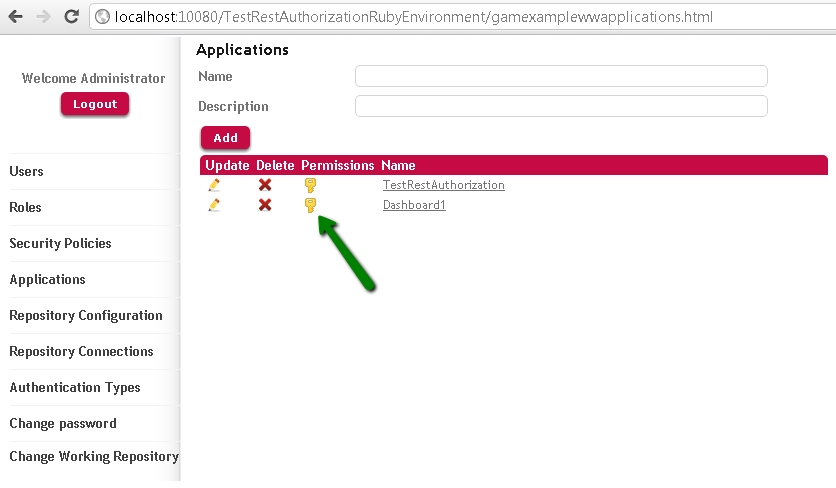
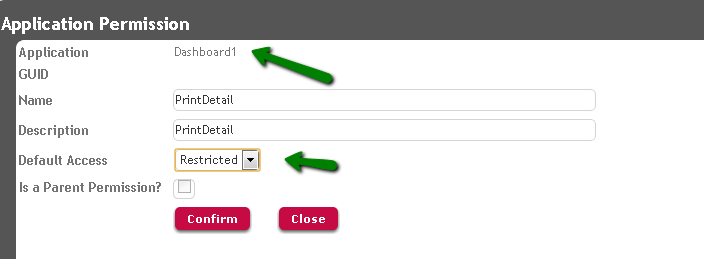
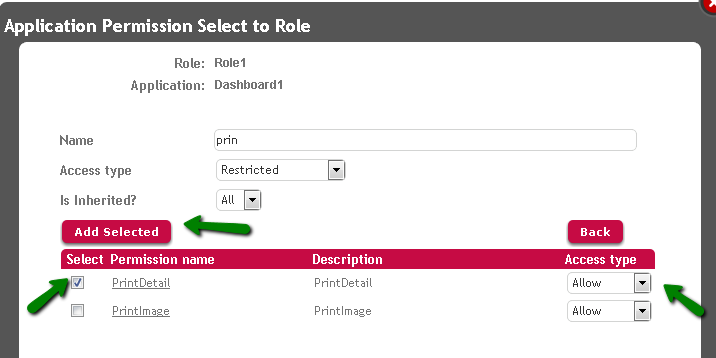
1. Define the permission named "PrintDetail" using the GAM Backend.
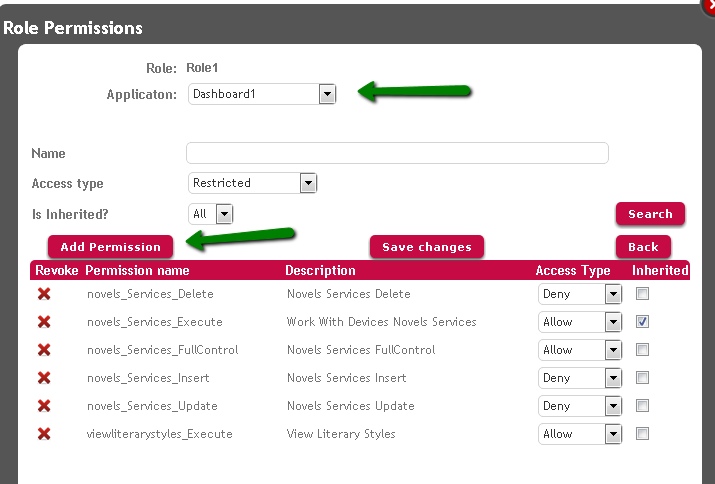
Go to WW Applications, select the corresponding application (in this example the SD application), and add to it the permission "PrintDetail", specifying the desired Default Permission Access Type. See the following figures:
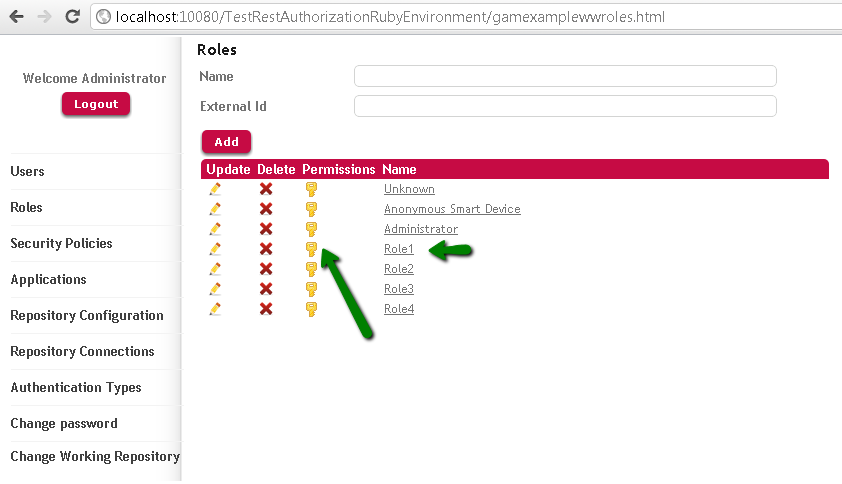
2. Define a role where this permission is included, with the corresponding Permission Access Type.
3. In the "Load Event" code of the SD panel, ask if the permission is included in the permissions granted to the user who executes, by coding the following:
&isAuthorized = GAMRepository.CheckPermission("PrintDetail")
if &isAuthorized
LiteraryStyleId.Visible = TRUE
else
LiteraryStyleId.Visible = FALSE
endif
Only users who have a role where the permission "PrintDetail" is allowed can view the LiteraryStyleId attribute in this example.
Note that there's no need to set the Integrated Security Level property to "Authorization", and that "Authentication" is enough.
GAM - Authorization Scenarios
Restricted access to GAM Backoffice
GAM - Permissions